In the previous article, we installed and configured Snort, and understood its basic functionalities. Today, we will explore Snort’s primary feature in respect to blue team operations, i.e. Snort as an Intrusion Detection System by writing effective rules. Snort’s ability to detect or prevent security incidents depends upon rules. Today we will see how to write effective rules to detect malicious or unintended traffic on a network. If you haven’t already read the previous article, please find it below:
Understanding Snort Rules Structure
Understanding Snort rules is essential to writing them. Snort rules follow a basic structure that must be adhered to while writing snort rules.
The rule structure is explained below:
- ACTION: Defines action to perform when the rule is matched. In context to Intrusion Detection, it is usually “alert”. If used as an Intrusion Prevention System, the “drop” or “reject” option is used. The difference between drop and reject options is that the drop option only terminates the specific packet for which the rule is matched, while the reject option terminates the entire connection with the host.
- PROTOCOL: Defined the type of traffic. At present, Snort supports TCP, UDP, ICMP, and IP traffic.
- SOURCE IP
- SOURCE PORT
- DIRECTION: The direction operator indicates the orientation of the traffic to which the rule applies. It is either “<>” which indicates bidirectional flow, or “→” which indicates source to destination flow.
- DESTINATION IP
- DESTINATION PORT
- RULE OPTIONS: The rule options define all other necessary details which make the rules more robust and meaningful. At the very least; Message, SID, and Revision Number have to be defined in rule options.
Anatomy of a Snort Rule
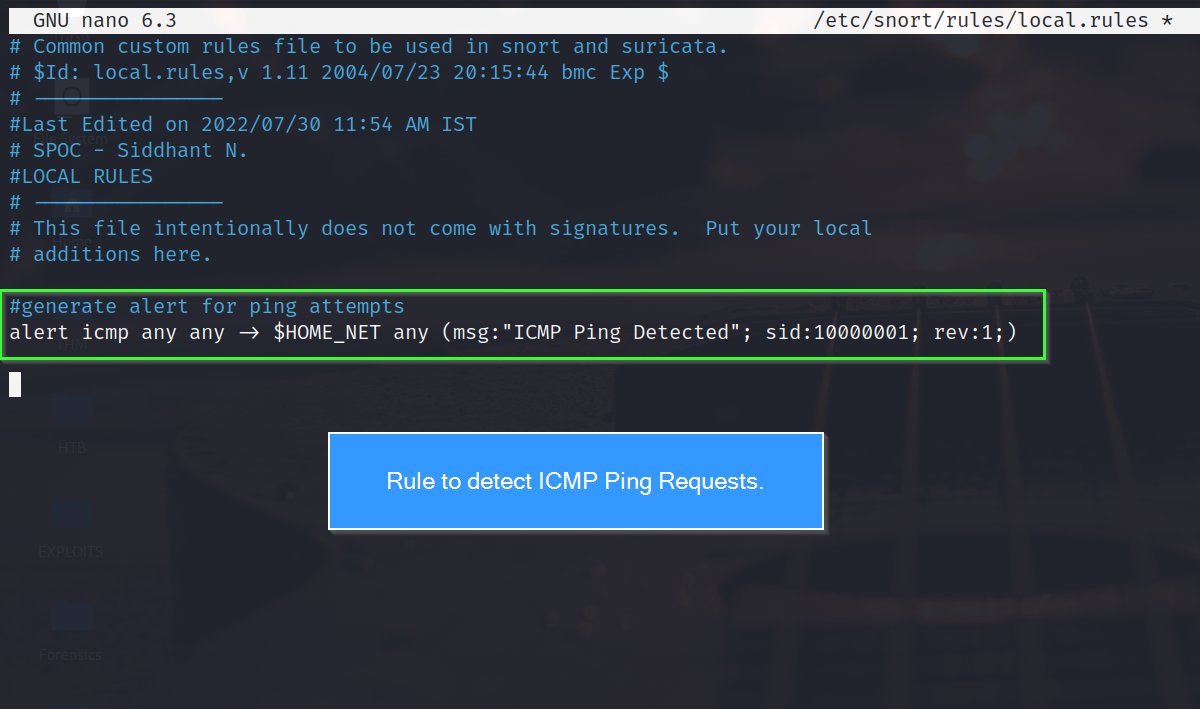
Now that we understand the rule structure, let’s take a look at a simple rule that detects ICMP Pings on the network.
alert icmp any any -> $HOME_NET any (msg:"ICMP Ping Detected"; sid:"1000001", rev:1)
Let’s break down the rule syntax bit by bit:
- alert: The rule will generate alerts when matched.
- icmp: Since we want to detect Ping requests, we choose the ICMP protocol.
- any: Requests coming from any host from any network.
- any: Requests coming from any port. Since Ping requests are not made from a standard port, we leave it to any.
- <>: Monitor all traffic, whether coming to or going from the internal network.
- any: Response sent from any port. Since Ping responses are not sent from a standard port, we leave it to any.
- msg: Specified alert message will be shown when the rule is matched.
- sid: Defines rule id. Each SID needs to be in the proper format. The format is mentioned below:
- <100: Reserved rules
- 100-999,999: Rules came with the build.
- >=1,000,000: Rules created by the user.
- rev: Defines revision id. Revision ID indicates the maturity of rules.
Intrusion Detection with Snort
sudo snort -q -c /etc/snort/snort.conf -i eth0 -A consoles
Writing Custom Snort Rules
- Snort Rule to detect FTP connection on a network
- Snort Rule to detect Failed FTP connections
- Snort Rule to detect TCP flags.
All 3 rules are practically demonstrated in a virtual network comprised of 2 virtual machines. One is Kali Linux 2022.3, and the other is Ubuntu Server 18.04. An FTP server is active on the Ubuntu server. Please remember the virtual network for the rest of the article.
#1 Snort Rule to Detect FTP Connections
alert tcp any any <> $HOME_NET 21 (msg:"FTP authentication attempt made"; sid:10000002; rev:1)
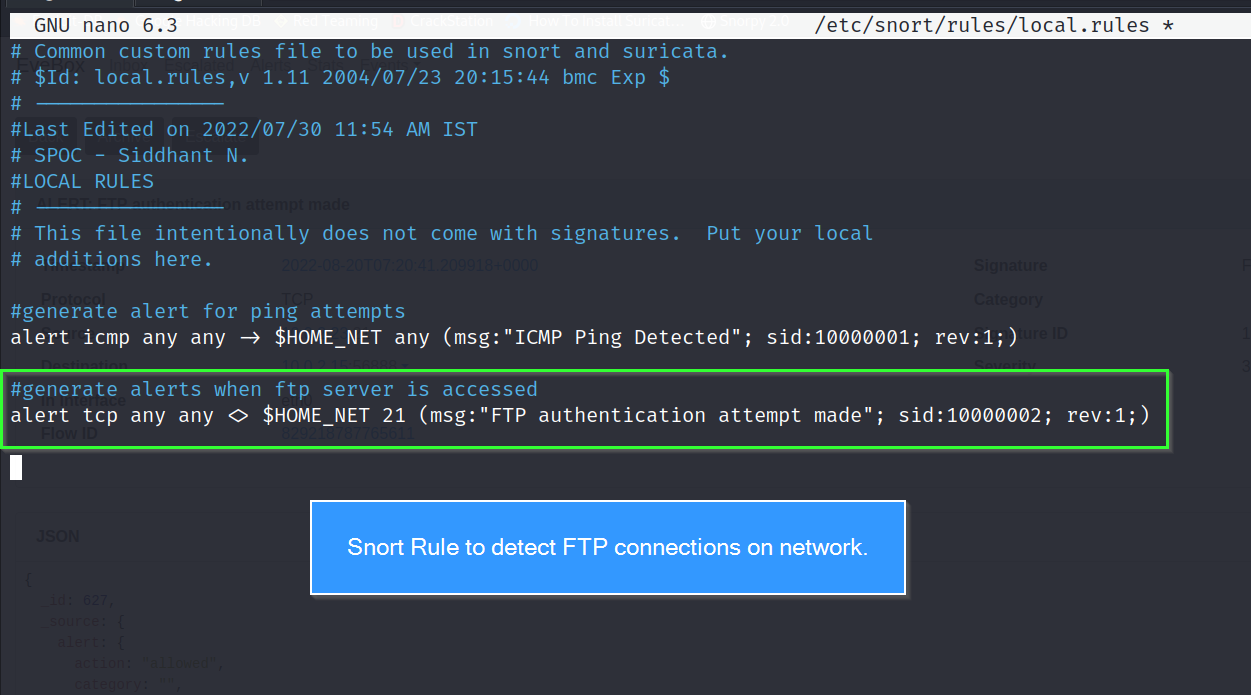
- alert: Generate an alert when the rule is matched.
- tcp: Since FTP is part of the TCP protocol suite.
- any: any host
- any: any port
- <>: bidirectional flow
- 21: Since FTP connections are established at port 21.
- msg: Display the specified message when the rule is matched.
#2 Snort Rule to Detect Failed FTP Connections
alert tcp any any <> $HOME_NET 21 (msg:"FTP authentication attempt failure"; content:"Login incorrect."; sid:1000003; rev:1;)
#3 Snort Rule to Detect TCP Flags
alert tcp any any -> $HOME_NET any (msg:"SYN Scan attempt"; flags:S; sid:1000004; rev:1;)
| Value | TCP Flag |
|---|---|
| F | FIN |
| S | SYN |
| R | RST |
| P | PSH |
| A | ACK |
| U | URG |


.png)